Technologies
What LastPass Subscribers Need to Do After the Latest Breach
Following the latest breach, you might want to find a new password manager.

LastPass, one of the world’s most popular password managers, is yet again under the microscope after its latest security breach.
In late December, LastPass CEO Karim Toubba acknowledged that a security incident the company first disclosed in August had ultimately paved the way for an unauthorized party to steal customer account information and vault data. This is the latest in a lengthy string of security incidents involving LastPass that date back to 2011.
It’s also the most alarming.
An unauthorized party now has access to unencrypted subscriber account information like LastPass usernames, company names, billing addresses, email addresses, phone numbers and IP addresses, according to Toubba. That same unauthorized party also has a copy of customer vault data, which includes unencrypted data like website URLs and encrypted data like the usernames and passwords for all the sites customers have saved in their vaults. If you’re a LastPass subscriber, the severity of this breach should have you looking for a different password manager because your passwords and personal data are at risk of being exposed.
What should LastPass subscribers do?
The company didn’t specify how many users were affected by the breach, and LastPass didn’t respond to CNET’s request for additional comment on the breach. But if you’re a LastPass subscriber, you need to operate under the assumption that your user and vault data are in the hands of an unauthorized party with ill intentions. Though the most sensitive data is encrypted, the problem is that the threat actor can run «brute force» attacks on those stolen local files. LastPass estimates it would take «millions of years» to guess your master password — if you’ve followed its best practices.
If you haven’t — or if you just want total peace of mind — you’ll need to spend some serious time and effort changing your individual passwords. And while you’re doing that, you’ll probably want to transition away from LastPass, too.
With that in mind, here’s what you need to do right now if you’re a LastPass subscriber:
1. Find a new password manager. Given LastPass’ history with security incidents and considering the severity of this latest breach, now’s a better time than ever to seek an alternative.
2. Change your most important site-level passwords immediately. This includes passwords for anything like online banking, financial records, internal company logins and medical information. Make sure these new passwords are strong and unique.
3. Change every single one of your other online passwords. It’s a good idea to change your passwords in order of importance here too. Start with changing the passwords to accounts like email and social media profiles, then you can start moving backward to other accounts that may not be as critical.
4. Enable two-factor authentication wherever possible. Once you’ve changed your passwords, make sure to enable 2FA on any online account that offers it. This will give you an added layer of protection by alerting you and requiring you to authorize each login attempt. That means even if someone ends up obtaining your new password, they shouldn’t be able to gain access to a given site without your secondary authenticating device (typically your phone).
5. Change your master password. Though this doesn’t change the threat level to the stolen vaults, it’s still prudent to help mitigate the threats of any potential future attack — that is, if you decide you want to stay with LastPass.
LastPass alternatives to consider
- Bitwarden: CNET’s top password manager is a highly secure and open-source LastPass alternative. Bitwarden’s free tier allows you to use the password manager across an unlimited number of devices across device types. Read our Bitwarden review.
- 1Password: Another excellent password manager that works seamlessly across platforms. 1Password doesn’t offer a free tier, but you can try it for free for 14 days.
- iCloud Keychain: Apple’s built-in password manager for iOS, iPadOS and MacOS devices is an excellent LastPass alternative available to Apple users at no additional cost. iCloud Keychain is secure and easy to set up and use across all of your Apple devices. It even offers a Windows client, too, with support for Chrome and Edge browsers.
How did it come to this?
In August 2022, LastPass published a blog post written by Toubba saying that the company «determined that an unauthorized party gained access to portions of the LastPass development environment through a single compromised developer account and took portions of source code and some proprietary LastPass technical information.»
At the time, Toubba said that the threat was contained after LastPass «engaged a leading cybersecurity and forensics firm» and implemented «enhanced security measures.» But that blog post would be updated several times over the following months as the scope of the breach gradually widened.
On Sept. 15, Toubba updated the blog post to notify customers that the company’s investigation into the incident had concluded.
«Our investigation revealed that the threat actor’s activity was limited to a four-day period in August 2022. During this timeframe, the LastPass security team detected the threat actor’s activity and then contained the incident,» Toubba said. «There is no evidence of any threat actor activity beyond the established timeline. We can also confirm that there is no evidence that this incident involved any access to customer data or encrypted password vaults.»
Toubba assured customers at the time that their passwords and personal data were safe in LastPass’s care.
However, it turned out that the unauthorized party was indeed ultimately able to access customer data. On Nov. 30, Toubba updated the blog post once again to alert customers that the company «determined that an unauthorized party, using information obtained in the August 2022 incident, was able to gain access to certain elements of our customers’ information.»
Then, on Dec. 22, Toubba issued a lengthy update to the blog post outlining the unnerving details regarding precisely what customer data the hackers were able to access in the breach. It was then that the full severity of the situation finally came to light and the public found out that LastPass customers’ personal data was in the hands of a threat actor and all of their passwords were at serious risk of being exposed.
Still, Toubba assured customers who follow LastPass’s best practices for passwords and have the latest default settings enabled that no further action on their part is recommended at this time since their «sensitive vault data, such as usernames and passwords, secure notes, attachments, and form-fill fields, remain safely encrypted based on LastPass’ Zero Knowledge architecture.»
However, Toubba warned that those who don’t have LastPass’s default settings enabled and don’t follow the password manager’s best practices are at greater risk of having their master passwords cracked. Toubba suggested that those users should consider changing the passwords of the websites they have stored.
What does all of this mean for LastPass subscribers?
The initial breach ended up allowing the unauthorized party to access sensitive user account data as well as vault data, which means that LastPass subscribers should be extremely concerned for the integrity of the data they have stored in their vaults and should be questioning LastPass’s capacity to keep their data safe.
If you’re a LastPass subscriber, an unauthorized party may have access to personal information like your LastPass username, email address, phone number, name and billing address. IP addresses used when accessing LastPass were also exposed in the breach, which means that the unauthorized party could also see the locations from which you used your account. And because LastPass doesn’t encrypt users’ stored website URLs, the unauthorized party can see all of the websites for which you have login information saved with the password manager (even if the passwords themselves are encrypted).
Information like this gives a potential attacker plenty of ammunition for launching a phishing attack and socially engineering their way to your account passwords. And if you have any password reset links stored that may still be active, an attacker can easily go ahead and create a new password for themselves.
LastPass says that encrypted vault data like usernames and passwords, secure notes and form-filled data that was stolen remains secured. However, if an attacker were to crack your master password at the time of the breach, they would be able to access all of that information, including all the usernames and passwords to your online accounts. If your master password wasn’t strong enough at the time of the breach, your passwords are especially at risk of being exposed.
Changing your master password now will, unfortunately, not help solve the issue because the attackers already have a copy of your vault that was encrypted using the master password you had in place at the time of the breach. This means the attackers essentially have an unlimited amount of time to crack that master password. That’s why the safest course of action is a site-by-site password reset for all of your LastPass-stored accounts. Once changed at the site level, that would mean the attackers would be getting your old, outdated passwords if they managed to crack the stolen encrypted vaults.
For more on staying secure online, here are data privacy tips digital security experts wish you knew and browser settings to change to better guard your information.
Technologies
Today’s NYT Mini Crossword Answers for Saturday, Feb. 28
Here are the answers for The New York Times Mini Crossword for Feb. 28.
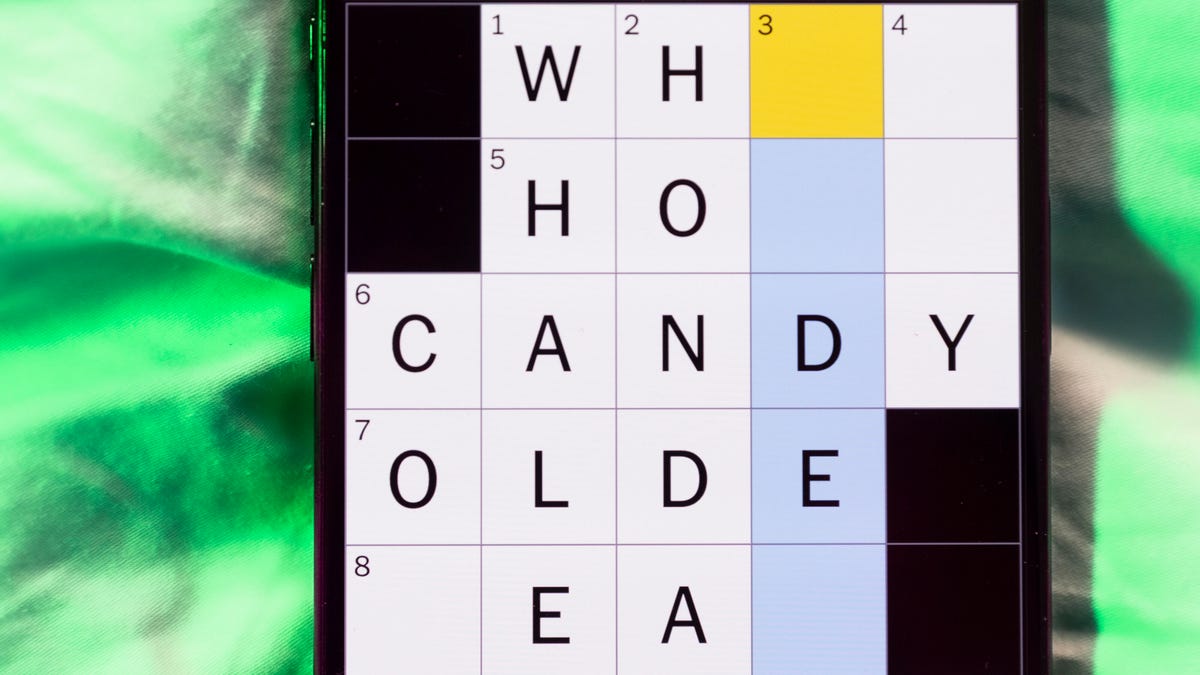
Looking for the most recent Mini Crossword answer? Click here for today’s Mini Crossword hints, as well as our daily answers and hints for The New York Times Wordle, Strands, Connections and Connections: Sports Edition puzzles.
Need some help with today’s Mini Crossword? As is usual for Saturday, it’s pretty long, and should take you longer than the normal Mini. A bunch of three-initial terms are used in this one. Read on for all the answers. And if you could use some hints and guidance for daily solving, check out our Mini Crossword tips.
If you’re looking for today’s Wordle, Connections, Connections: Sports Edition and Strands answers, you can visit CNET’s NYT puzzle hints page.
Read more: Tips and Tricks for Solving The New York Times Mini Crossword
Let’s get to those Mini Crossword clues and answers.
Mini across clues and answers
1A clue: Rock’s ___ Leppard
Answer: DEF
4A clue: Cry a river
Answer: SOB
7A clue: Clean Air Act org.
Answer: EPA
8A clue: Org. that pays the Bills?
Answer: NFL
9A clue: Nintendo console with motion sensors
Answer: WII
10A clue: ___-quoted (frequently said)
Answer: OFT
11A clue: With 13-Across, narrow gap between the underside of a house and the ground
Answer: CRAWL
13A clue: See 11-Across
Answer: SPACE
14A clue: Young lady
Answer: GAL
15A clue: Ooh and ___
Answer: AAH
17A clue: Sports org. for Scottie Scheffler
Answer: PGA
18A clue: «Hey, just an F.Y.I. …,» informally
Answer: PSA
19A clue: When doubled, nickname for singer Swift
Answer: TAY
20A clue: Socially timid
Answer: SHY
Mini down clues and answers
1D clue: Morning moisture
Answer: DEW
2D clue: «Game of Thrones» or Homer’s «Odyssey»
Answer: EPICSAGA
3D clue: Good sportsmanship
Answer: FAIRPLAY
4D clue: White mountain toppers
Answer: SNOWCAPS
5D clue: Unrestrained, as a dog at a park
Answer: OFFLEASH
6D clue: Sandwich that might be served «triple-decker»
Answer: BLT
12D clue: Common battery type
Answer: AA
14D clue: Chat___
Answer: GPT
16D clue: It’s for horses, in a classic joke punchline
Answer: HAY
Technologies
Ultrahuman Ring Pro Brings Better Battery Life, More Action and Analysis
The company’s new flagship smart ring stores more data, too. But that doesn’t really help Americans.

Sick of your smart ring’s battery not holding up? Ultrahuman’s new $479 Ring Pro smart ring, unveiled on Friday, offers up to 15 days of battery life on a single charge. The Ring Pro joins the company’s $349 Ring Air, which boosts health tracking, thanks to longer battery life, increased data storage, improved speed and accuracy and a new heart-rate sensing architecture. The ring works in conjunction with the latest Pro charging case.
Ultrahuman also launched its Jade AI, which can act as an agent based on analysis of current and historical health data. Jade can synthesize data from across the company’s products and is compatible with its Rings.
«With industry-leading hardware paired with Jade biointelligence AI, users can now take real-time actionable interventions towards their health than ever before,» said Mohit Kumar, CEO of Ultrahuman.
No US sales
That hardware isn’t available in the US, though, thanks to the ongoing ban on Ultrahuman’s Rings sales here, stemming from a patent dispute with its competitor, Oura Ring. It’s available for preorder now everywhere else and is slated to ship in March. Jade’s available globally.
Ultrahuman says the Ring Pro boosts battery life to about 15 days in Chill mode — up to 12 days in Turbo — compared to a maximum of six days for the Air. The Pro charger’s battery stores enough for another 45 days, which you top off with Qi-compatible wireless charging. In addition, the case incorporates locator technology via the app and a speaker, as well as usability features such as haptic notifications and a power LED.
The ring can also retain up to 250 days of data versus less than a week for the cheaper model. Ultrahuman redesigned the heart-rate sensor for better signal quality. An upgraded processor improves the accuracy of the local machine learning and overall speed.
It’s offered in gold, silver, black and titanium finishes, with available sizes ranging from 5 to 14.
Jade’s Deep Research Mode is the cross-ecosystem analysis feature, which aggregates data from Ring and Blood Vision and the company’s subscription services, Home and M1 CGM, to provide historical trends, offer current recommendations and flag potential issues, as well as trigger activities such as A-fib detection. Ultrahuman plans to expand its capabilities to include health-adjacent activities, such as ordering food.
Some new apps are also available for the company’s PowerPlug add-on platform, including capabilities such as tracking GLP-1 effects, snoring and respiratory analysis and migraine management tools.
Technologies
The FCC Just Approved Charter’s $34.5B Cox Purchase. Here’s What It Means for 37M Customers
-
 Technologies3 года ago
Technologies3 года agoTech Companies Need to Be Held Accountable for Security, Experts Say
-

 Technologies3 года ago
Technologies3 года agoBest Handheld Game Console in 2023
-

 Technologies3 года ago
Technologies3 года agoTighten Up Your VR Game With the Best Head Straps for Quest 2
-

 Technologies4 года ago
Technologies4 года agoBlack Friday 2021: The best deals on TVs, headphones, kitchenware, and more
-

 Technologies5 лет ago
Technologies5 лет agoGoogle to require vaccinations as Silicon Valley rethinks return-to-office policies
-

 Technologies5 лет ago
Technologies5 лет agoVerum, Wickr and Threema: next generation secured messengers
-

 Technologies4 года ago
Technologies4 года agoOlivia Harlan Dekker for Verum Messenger
-

 Technologies4 года ago
Technologies4 года agoiPhone 13 event: How to watch Apple’s big announcement tomorrow
